The Problem
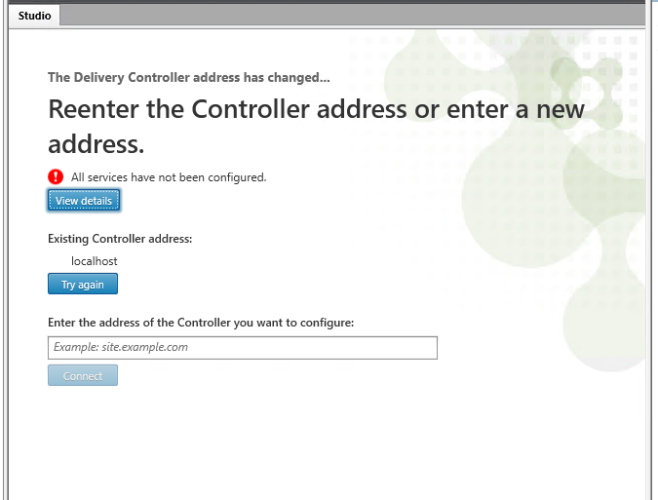
At a customer site we were experiencing a problem where we are unable to open Citrix Studio. Citrix Studio reported the error ‘Reenter the controller address or enter a new address‘ and ‘all services have not been configured‘. Looking in to the error log it seems that an upgrade of the Citrix database has failed, but we did not do any update of Citrix.
Since we do not login to the DDC every day and the use of Studio is not a daily thing, this error could have been there for a while. We were not able to find a cause of this error directly.
The error log shows the following. The full output is available here.
Reset-ProvEnabledFeatureList -AdminAddress “customersite.local:80” -BearerToken ********
Reset-ProvEnabledFeatureList : The operation could not be completed as the database has not been configured for the Citrix Machine Creation Service service.
Citrix.XDPowerShell.Status.DatabaseNotConfigured,Citrix.MachineCreation.Sdk.FeatureChecks.Commands.ResetProvEnabledFeatureListCommand
StackTrace: Citrix.Orchestration.Base.LogicModels.Exceptions.InvalidServiceConfigurationException All services have not been configured.
StackTrace: System.InvalidOperationException The operation could not be completed as the database has not been configured for the Citrix Machine Creation Service service.
at System.Management.Automation.MshCommandRuntime.ThrowTerminatingError(ErrorRecord errorRecord)
This is a customer site with a single Citrix Delivery Controller on version 1912 CU2 and is also running other Citrix services like Storefront, Director, Licensing and has a local Microsoft SQL Express database. The Server OS is Windows Server 2019 1809 17763.1935.
We could not find a way to fix this issue without installing a new Delivery Controller. We created a Citrix case and they could not find the exact cause of this issue and they recommended us to recreate the environment with a new database. We saw no other choice to do so, but after a while the same error returned on a clean install. A new Citrix case was created..
The Research
Citrix support first tried to recreate the database connection strings without any luck. To do this, they pointed to this Citrix article with a few powershell scripts. This article and scripts can be a great help when resetting the connection strings or moving to a new database location.
At first, Citrix support pointed to a problem within the SQL database because of an ‘Monitor.GetSchemaVersion: Could not find stored procedure ‘Monitor.GetSchemaVersion’‘ when testing the database connections. This was a false positive we also found at other customer sites.
The CDF trace pointed us to the following error, which also suggested that there was a problem with the SQL database
13632,2,2021/07/28 15:29:49:47119,16044,16388,Unknown,-1,Xendesktop Management Console,,0,,1,Error,”DatabaseUpgradeTask(482): Upgrade database analysis error: Citrix.Orchestration.Base.LogicModels.Exceptions.ScriptException: Database connection not set.
18418,2,2021/07/28 15:29:49:92234,20400,4272,Citrix.MachineCreation.exe,0,MachineCreationDAL,,0,,1,Error,”[TID:dcda976b-efa7-11eb-8175-0f695eca111d]The database for the service is not configured.”,””
We looked futher in to the SQL database and concluded that it was working fine. The stored procedure was OK and the database seemed to working fine. Restoring a backup of the database from way before the issue occurred, did not solve the problem. We gatherd more CDF traces and ProcMon traces and after a lot of research from Citrix Support we came to a conclusion which solved this error and the Citrix case.
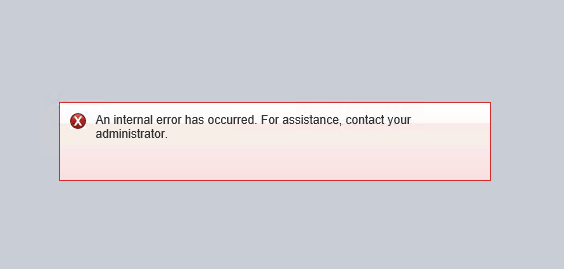
Not sure if it was caused by changes during research but Citrix Director also began showing errors and now we are unable to manage the environment using Studio and Director.
Your logon attempt was unsuccessful.
Username: ‘xxx’
Domain: ‘xxxx’
Additional information:
‘Xen Desktop Controllers is running an incompatible version of the software. For assistance, contact your administrator.‘
The Solution
Citrix Support reviewed the logs and found an issue with the performance counter that is causing this issue with Citrix Studio and Citrix Director:
2341,1,2021/10/01 13:57:36:72314,13396,2748,Citrix.MachineCreation.exe,0,MachineCreationDAL,,0,,1,Error,”ERROR: DALRuntime: Performance counter initialization failed: System.InvalidOperationException: The requested Performance Counter is not a custom counter, it has to be initialized as ReadOnly.
2502,3,2021/10/01 13:57:38:25555,13396,2748,Citrix.MachineCreation.exe,0,MachineCreationLog,,0,,1,Error,”Exception thrown Starting DAL: System.InvalidOperationException: The requested Performance Counter is not a custom counter, it has to be initialized as ReadOnly.
In the above logs the DAL stands for data access layer, which is our SQL access layer. This failure of the performance counter is causing the failure in initialization of the DAL and hence we see the Database configuration error.
I ran the following commands on request of Citrix support and Citrix Studio and Director were up and running again:
unlodctr “Windows Workflow Foundation 4.0.0.0”
lodctr C:\Windows\INF\Windows Workflow Foundation 4.0.0.0\PerfCounters.ini
unlodctr “.NET Data Provider for SqlServer”
lodctr C:\Windows\INF\.NET Data Provider for SqlServer\_dataperfcounters_shared12_neutral.ini
unlodctr “.NETFramework“
lodctr C:\Windows\INF\.NETFramework\corperfmonsymbols.ini
We did not find a root cause of the performance counter issue but this solved the error in Citrix Studio for us. The error that was shown was caused by an issue with one of the above performance counters and could have been caused by a software install or (Windows) update.